•They were tortured, forcefully married out and remarried again when troops killed their first husbands
• We tricked the terrorists to escape from the camp
• I walked for hours through deadly forest under harsh condition —Mary
• I slept under a tree with my child through the night while escaping —Hauwa
• More than 20 of our classmates still in Gazuwa camp, Sambisa forest
By Ndahi Marama, Maiduguri
It was like tales by moon light when news broke on April 14, 2014 that 276 girls of Government Secondary School, Cbibok, Borno State had been abducted by Boko Haram insurgents and herded into the forest like cattle. Many doubted that a thing like that could happen under the nose of our security men. This may have accounted for why the troops did not react immediately by chasing them before they could go farther into the forest.
Few of the girls however braved the odds by jumping down from the trucks conveying them and disappeared into the forest before they found their way back home. The girls were kept in the terrorists’ camp like cattle, tortured and turned to sex slaves. They were traumatized. Many were forcefully married off. For eight years they were held captive under terrible conditions in the various camps known to the military whose reason for not daring to storm the camps and rescue the girls was to avoid collateral damage to the captives. Left to their fate, some of the girls summoned courage to escape from the camp in the dead of the night, battling snakes and other wild animals as they ran for freedom.
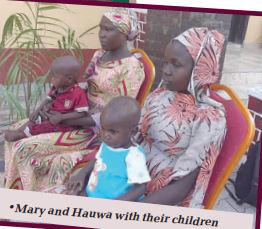
Last Tuesday, two of the Chibok Secondary School girls, Mary Dauda and Hauwa Joseph, who were among the 276 students abducted on April 14, 2014 and had been in captivity for eight years, tricked their way to escape from the camp. Before they were abducted, they were teenagers. They were innocent. But they were forcefully married to the terrorists in the camp. Both are now nursing a child each.
Narrating their experiences while in captivity, Mary and Hauwa who both appeared traumatized revealed that more than 20 of their abducted classmates are still in Gazuwa camp in Sambisa forest.
Saturday Vanguard checks indicated that Gazuwa camp, is one of the acclaimed headquarters of the Jam’at Ahl as-Sunnah lid-Da’wah wa’l-Jihd, Boko Haram faction, formerly known as Gabchari, Mantari and Mallum Masari, which is located about nine kilometres to Bama Local Government Area of Borno State.
Mary Dauda, who recounted her experience in the hands of the insurgents, said she could still vividly recall her forceful marriage eight years ago after she was abducted at the age of 18 years. She said she walked through the deadly forest for many days before she eventually found help.
She also said, it was a very tough time for her while in captivity, especially as she was tortured whenever she refused to pray according to Islamic injunction or refused to heed to the ideologies of the terrorists. Like the others conscripted by the terrorists, she had been told that she would be hunted down and killed if she tried to escape. But she eventually made the attempt to escape. She succeeded. And today she is free from the captivity of the terrorists even as she felt for her classmates whom she left behind in the camp.
Mary’s journey to freedom
“I took excuse from Malam Ahmed (her terrorist husband) that I will be visiting my relative from Chibok in the town of Ngoshe and he granted me one week. That was when I began my journey to freedom. I left Sabil Huda, popularly known as the camp of Abubakar Shekau and proceeded towards Njimiya and Parisu, where I met some of the Mujahedeens. They asked where I was going to and I told them I was granted permission to visit my sister in Ngoshe.
“I finally arrived Gava village in Gwoza, after walking for many hours through the deadly forest under harsh condition. I asked some people to direct me to the home of the daughter of Chibok girl. After meeting her, I told her of my plans to return home and she told me she would have wanted to come with me but her husband had placed her on strict surveillance for attempting to escape. I then left her and proceeded towards Ngoshe town.
“On my way, I met an old man who promised to help me to escape. But he told me that it would not be possible in the afternoon and that we should wait until the sun had set. At about 8pm, he took me to Ngoshe town and asked me to pass the night in the outskirts of the town before proceeding the next morning. This was because I may be suspected to be a suicide bomber and would have been killed or fired at by the troops if I entered in the night. When the day broke, I reported myself to some soldiers where I was taken care of with my baby.” she said.
How I tricked the terrorists —Hauwa
On her part, Hauwa Joseph said she was forcefully married to Amir Abbah, Commander of Boko Haram (Munzul), at Gazuwa camp who was later killed during an encounter with the troops of the Nigerian Army. She said she voluntarily escaped from the camp of the terrorists during massive incursion of the troops of the Nigerian Army into their camp in Gazuwa on June 12 this year.
She said as people were running in the same direction where the sect members were hiding women and children, she took a separate route to escape from the terrorists’ camp. She said on her way, she met some of the insurgents who asked her where she was going, but she tricked them and told them that she was following some women to hide in the nearby forest.
“I slept under the tree with my child, then proceeded the next day until I arrived the road where I approached a military check point. Initially, the soldiers thought I was a suicide bomber, but when I explained how I escaped from the terrorists, they took me along with them.”
We have decimated dozens of terrorists—Military
Last Tuesday, the Theatre Commander, Joint Taskforce Northeast ‘Operation HADIN KAI’ Major General Christopher Musa handed over the two Chibok school girls to the Borno State Government.
On the list of the over 250 missing Chibok girls compiled by the government, Hauwa Joseph was listed as serial number 18, while Mary Dauda is serial number 46. Each of the rescued girls is nursing a baby of about one and a half years old. They were remarried to another terrorists after troops killed their first husbands.
Briefing Journalists at Headquarters Theatre Command, Maimalari Cantonment Maiduguri, the Theatre Commander, Major General Musa said, concerted efforts were being put in place to rescue the remaining Chibok girls and all those who were still under the captivity of terrorists in the region.
He said, “apart from rescuing these two Chibok girls with their children, we have also decimated dozens of terrorists who have been hiding in the Sambisa forest, especially the Timbuktu Triangle during our fighting patrols.
“As the rainy season set in and a lot of farmers are willing to go to their farms, we will work tirelessly to provide safety of our farmers in their farming activities. But we want to appeal that the farmers should be wary of some planted Improvised Explosive Devices (IEDs) by terrorists in some areas, even though, the military is doing everything possible to clear most of the places suspected to have unexploded IEDs planted by terrorists in the region.
“I want to also appeal to the State Government and other philanthropic organisations to assist farmers with agricultural inputs or farming tools to boost the morale of the teaming farmers who have since relocated to their liberated communities.”
On the reopening of the 185km Maiduguri-Damboa-Biu road which was closed to motorists some years ago, General Musa said troops were combing the road which passed through the sambisa forest. He appealed to Borno State Government and other Non- Governmental Organisations, NGOs to collaborate with troops to fix some portions of the road for easy access, as troops continue clearance of unexploded IEDs planted along the road.
Speaking on how the Chibok girls were rescued, the General Officer Commanding 7 Division, Major General Waidi Shaibu said, Hauwa Joseph was rescued with her child on the 12th June, 2022 in Bama local government area, while Mary Dauda was rescued with her child around Ngoshe community of Gwoza Local Government Area of the state on 14th June same year during troops’ fighting patrol in the Division Area of Responsibility.
General Shaibu said, all the girls and their children have undergone proper medical check- up and treatment before handing them over to the Government that would subsequently reunite them with their parents.



Leave A Comment